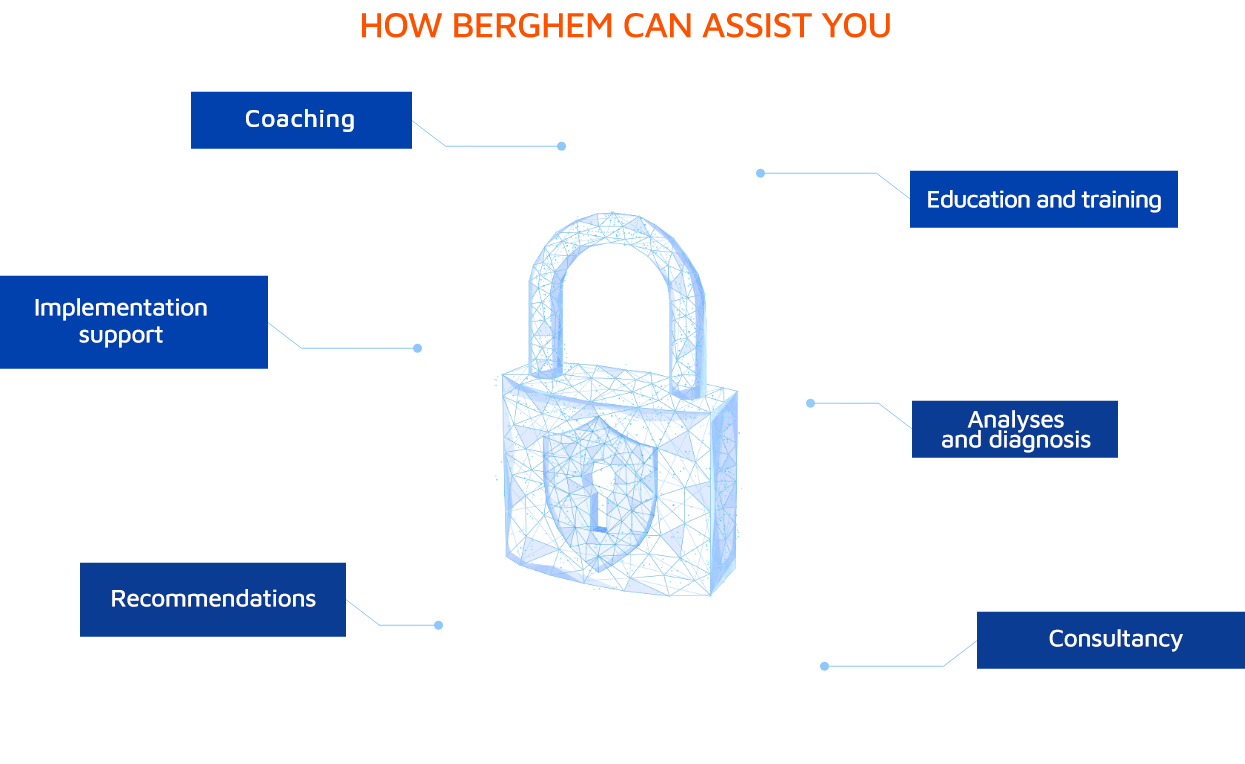
Rely on Berghem to assist you in keeping the information and assets of your company, customers, executives and other stakeholders secure.
[email protected] +55 11 2391-5745
VULNERABILITY ASSESSMENTS AND PENTESTS
Penetration testing on the application or business infrastructure layer, such as: network, wireless, servers and devices.
We simulate actions by hackers and users of the system who are looking to compromise the security of applications and environments, obtain critical data and either corrupt or deceive it, and other malicious intentions.
Technical and management level reports are generated from broad and combined reconnaissance, identification and attack efforts – with subsequent recommendations on remediation and improvements.
While a Pentest involves manual, physical, and automated attempts to exploit, including through the use of social engineering, a vulnerability analysis is generally not intended to exploit, but to identify gaps in security systems and policies.

Our procedures are conducted using proprietary methodology that has been developed and refined over 15 years of activities using the latest findings and best practices in the area of security.